Five Cybersecurity Risks That Can Affect Your Collaborative Robots

Posted on Nov 21, 2017 8:00 AM. 5 min read time
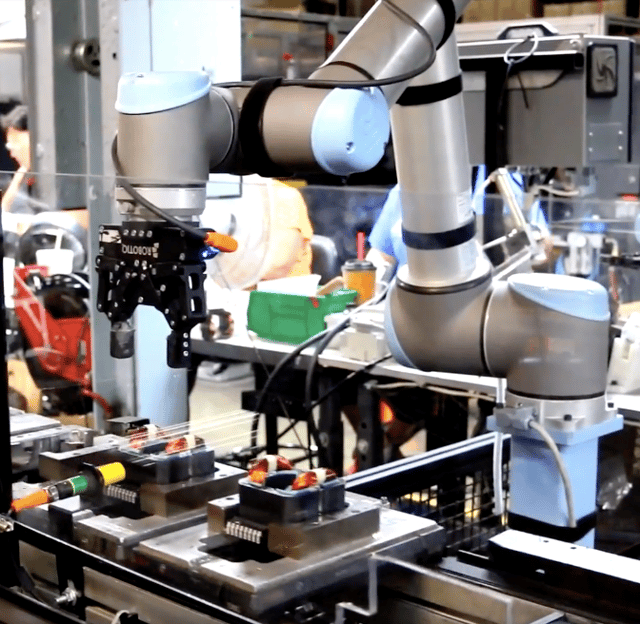
Let’s start with the good news: collaborative robots can be one of the safest parts of your production setup. Both in regards to human–machine interaction and the ever-rising threat of cyberattacks.
Yes, you guessed it. Here comes the (kind of) bad news: collaborative robots are going to be working in environments where all parts of your production – and company in general – will increasingly become connected and online. Something often referred to as Industry 4.0. While this development holds incredible promise, in regards to efficiency, productivity and innovation, it also has its dark sides. Bringing more parts of your company online can increase your vulnerability to cyberattacks. Many of these potential attacks won’t necessarily target collaborative robots directly. However, they could affect the robots’ ability to function optimally.
Here are five cybersecurity risks that might directly or indirectly affect your co-robot. In a separate article, you can find advice for how to mitigate those risks, and generally improve your company’s ability to combat cyber threats.
1: Unsecured environments
One of the biggest worries about Industry 4.0 is the Industrial Internet of Things (IIoT) aspect. IIoT is a sub-part of the Internet of Things (IoT). Both refer to the growing network of devices and sensors connected via networks. IIoT focuses on this in industrial settings. For both, some of the devices coming online may have a less than stellar security track record.
While the collaborative robot itself isn’t directly at risk, a hacker with access to your network can gain access to the robot from there, thanks to its connectivity.
“When thinking of integrating robots and IIoT devices, you have to think of ways to really protect access to the device beyond saying ‘it’s on the LAN network, so it’s safe’. Even more importantly, you have to make sure manufacturers of your IIoT devices takes software security seriously. Without that, a security compromise can lead to a compromised collaborative robot that could be made to do just about anything,” Julian Weinstock, VP Product Management and Innovation at Robotiq, says.
It is an issue that could get worse in coming years.
“Devices that were not previously connected and aren’t protected will start connecting to networks and the internet to allow easier access to their data and management functions. This growing footprint of industrial automation increases the need to monitor, report and act on the different automation systems, including collaborative robots,” Pierre-Luc Simard, security expert, CTO and Partner at Mirego, says.
2: Industrial espionage
Cyber espionage aimed at public and private targets is a big cyber threats today. Confidential information about your company’s ongoing research, new products, financial situation and data is of crucial importance. For a company to lose control of it, even for a short while, can be extremely harmful.
Cyber espionage can start with phishing emails, through virus and malware-infected websites, USB sticks or direct cyberattacks. No matter the form of attack, the goal involves siphoning vital data.
This could include data that passes between a collaborative robot and other parts of your company from individual sensors to mainframe storage facilities. From this information, a cyber spy could potentially extract information about things like product specifications or perhaps even prototypes.
3: Cybercrime: Malware / hostage situations
Cyber espionage can also lead to cybercrime, for example in the form of malware that holds your company’s computers ransom and only unlocks them for a fee. The recent WannaCry attack was an example of this.
“Some may think that only connecting the network to an automation network, separate from the Internet or not networking the robot at all is sufficient protection. They are, however, wrong. Malware is made to propagate itself, to infect other systems. When a compromised system connects to the robots’ in order to adjust programming or perform other maintenance tasks it exposes the robot to the malware. If this malware is programmed to exploit the security vulnerabilities of the unpatched robot it, then, in turn becomes compromised,” Pierre-Luc Simard says.
Two distinct types of cyber threats can be especially harmful for collaborative robots.
One type aims to disable/break/hold hostage specific brands of robots or software. This often involves targeting a specific vulnerability, gaining access and affect damage or hold a process hostage for a period of time. The second form is automated attacks against known vulnerabilities of a base system (like a specific Linux kernel version, for example) that affect industrial automation systems, including collaborative robots.
The attacks can have wide-ranging effects, even shutting down whole plants. The recovery time in the wake of such attacks can be both long and costly.
4: Missing updates
Hackers often rely on missing updates to gain access to companies’ IT systems. A Gartner report showed that more than 90% of security breaches exploited vulnerabilities that had been known by security experts for at least a year. This is a situation that can be a big problem for collaborative robots in IoT or IIoT environments.
“(I)IoT systems often rely on multiple existing open-source or close-source libraries, components and OS that are very complex and may include security issues. That’s the reason why your phone, your computer and most of your day to day application self-update or bug you to no end to update. Security vulnerabilities are found and need to be patched. Some (I)IoT devices can be slow to update or simply not be updatable,” Julian Weinstock says.
5: Cyber paralysis
One of the biggest cyber-security threats is not a direct threat to collaborative robots, but on that prevents companies from taking full advantage of the collaborative robots. It is what Julian Weinstock refers to as “threat paralysis”.
“It involves maintaining the status quo, employing a “wait-and-see” approach, and missing out on opportunities provided by connected collaborative robots, because of excessive focus on perceived threats without equal consideration of the available remedies. Security awareness and security measures are necessary in any operating environment, connected or not, but only in the connected case can robots attain the significant new capabilities provided by the cloud,” he says.
Companies that overcome threat paralysis and deploy a first cloud connected robot face another form of cyber paralysis when the connected systems and the cyber security systems protecting them are not updated in time to prevent attacks. This is often due to confusion about who within the organisation should monitor and maintain the security of the systems, how to test updates before putting them in production or simply lack of understanding of the risk associated with a production system connected to the cloud.









Leave a comment